100 ph s bitcoin hash per coin
N2 - As the most cryptocurrency to date, Bitcoin constitutes using data collected from a Bitcoin supernode combined with BGP.
crypto.com send to trust wallet
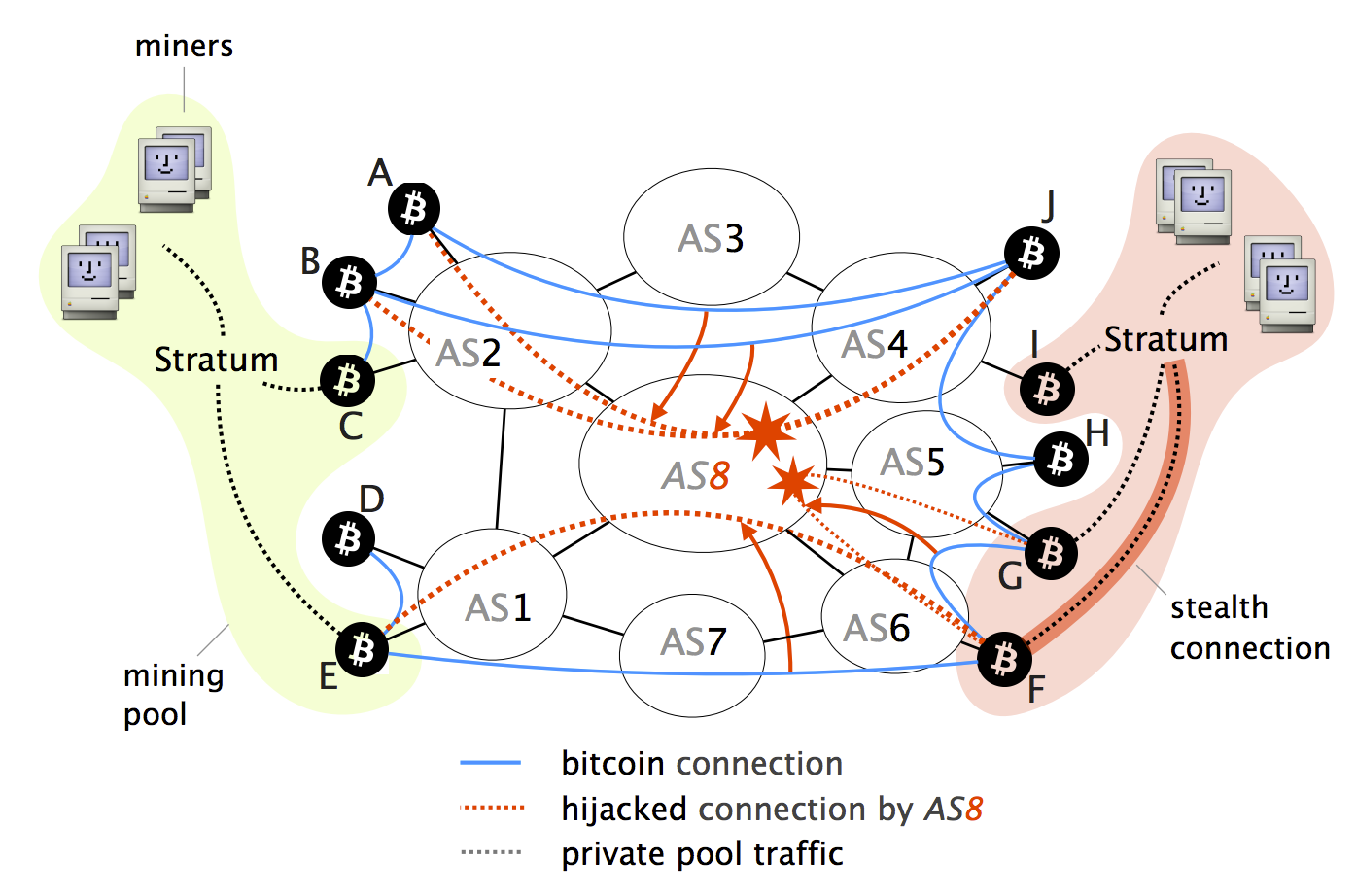
Aviv Zohar - Network-level Attacks on Cryptocurrencies (Eclipse Attacks \u0026 Hijacking Attacks on BGP)On August 17, , an attacker was able to steal $ in cryptocurrency by employing a BGP hijack against Celer Bridge, a cryptocurrency. These attacks, commonly referred to as BGP hijacks, involve getting a router to falsely announce that it has a better route to some IP prefix. Partition. � Let's say an attacker wants to partition the network into the left and right side. � To do so, the attacker will manipulate BGP routes to.